We all have a tendency to avoid our weaknesses. When we do that, we never progress or get any better.
Jocko Willink
In today’s rapidly evolving landscape of cybersecurity, organizations are increasingly recognizing the critical importance of fortifying their defences. Despite substantial investments worldwide to repel digital threats, malicious actors persistently exploit vulnerabilities, even within the most fortified systems. Their primary focus? Employees. These individuals are regarded by cybercriminals as the weakest link in the cybersecurity chain. However, a solution exists—a beacon of hope in the form of a “beefed-up” security awareness training.
Enhancing security awareness among employees is undeniably a top priority. In this article, we will delve into the motivations behind cybercriminals’ fixation on employees and explore the profound implications of enriching their security knowledge. By acknowledging vulnerabilities and taking proactive measures, businesses can significantly reduce risks and empower their workforce to effectively counter cyber threats.
The Vulnerabilities Within – Identifying the Challenges
Does your organization grapple with these common challenges?
1. Lack of Awareness: The unfortunate reality is that many employees remain unfamiliar with cybersecurity hazards, tactics used by cybercriminals, and essential best practices. Malicious actors exploit this knowledge gap to launch deceptive campaigns, distribute malicious software, and orchestrate elaborate social manipulation tactics.
2. Privileged Access: Employees often possess access to critical systems, sensitive data, and administrative privileges coveted by cybercriminals. Breaching these accounts can provide malicious agents with access to valuable assets, leading to significant disruptions.
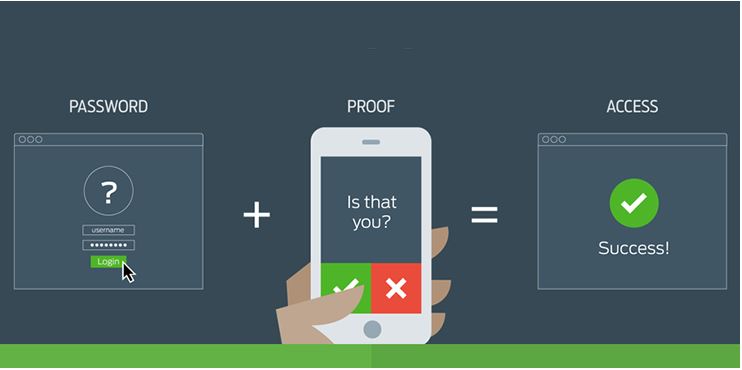
3. Social Manipulation: Cybercriminals excel at manipulating human emotions, trust, and curiosity. They employ these tactics to coerce employees into divulging confidential information, sharing login credentials, or unknowingly compromising security protocols.
4. BYOD Risks: The “Bring Your Own Device” (BYOD) trend introduces additional risks to businesses. Personal devices lacking robust security measures create vulnerabilities that cybercriminals are eager to exploit.
5. Remote and Hybrid Work Challenges: The shift to remote and hybrid work environments presents novel challenges. Home networks with weaker security, shared devices, and domestic distractions make employees more susceptible to digital attacks.
Constructing a Cyber-Resilient Workforce: Best Practices
To build a solid foundation for cyber resilience within your organization, consider these best practices:
1. Assess the Landscape: Gain a deep understanding of the specific cybersecurity risks your organization faces. Identify areas where employees are most vulnerable.
2. Define Objectives: Clearly define the knowledge and skills your employees need to acquire through your security awareness program.
3. Develop Engaging Content: Craft compelling content that captivates your employees’ attention and seamlessly integrates cybersecurity concepts. Use real-world scenarios to instill cybersecurity wisdom.
4. Tailor Content: Customize your content to address unique challenges within your organization. Align the material with employees’ roles and responsibilities.
5. Embrace Continuity: Establish a consistent rhythm of instruction to reinforce cybersecurity principles. Keep your workforce updated on emerging threats and countermeasures.
6. Measure Effectiveness: Regularly assess the impact of your security awareness program through behavioural outcomes, evaluations, and feedback. Use data to refine and improve your program continuously.
7. Foster a Cybersecurity Culture: Encourage proactive engagement by fostering open communication, providing spaces for incident reporting, and emphasizing shared responsibility for protecting the digital realm.
Uniting for a Secure Future
We stand united in our mission to usher in a new era of digital guardianship. Let us seize this opportunity to transform our employees into an unwavering bulwark against cyber threats. The investment in employee security awareness serves as the crucible in which our defences are honed, ensuring a future marked by unwavering resilience. As the cybersecurity landscape evolves, the empowerment of our workforce will prove instrumental in safeguarding our business from the persistent threats of the digital age.